An
NSA-derived ransomware worm is shutting down computers worldwide
Wcry uses weapons-grade exploit published by the NSA-leaking Shadow Brokers
12 May, 2017
A highly virulent new
strain of self-replicating ransomware is shutting down computers all
over the world, in part by appropriating a National Security Agency
exploit that was publicly released last month by the mysterious group
calling itself Shadow Brokers.
The malware, known as
Wanna, Wannacry, or Wcry, has infected
at least 75,000 computers,
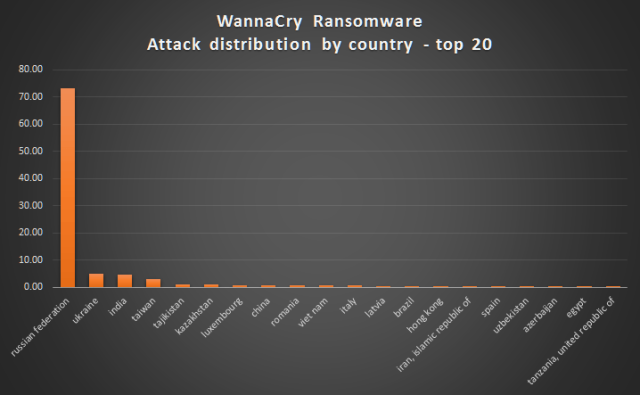
according to antivirus provider Avast. AV provider Kaspersky Lab
said organizations
in at least 74 countries have been affected,
with Russia being disproportionately affected, followed by Ukraine,
India, and Taiwan. Infections are also spreading
through the United States.
The malware is notable for its multi-lingual ransom demands,
which support
more than two-dozen languages.
Wcry is reportedly
causing disruptions at banks, hospitals, telecommunications services,
and other mission-critical organizations in multiple countries,
including the UK, Spain, Germany, and Turkey. FedEx, the UK
government's National Health Service, and Spanish telecom Telefonica
have all been hit. The Spanish
CERT has called it a
"massive ransomware attack" that is encrypting all the
files of entire networks and spreading laterally through
organizations.
Remember Code Red?
Another
cause for concern: wcry copies a weapons-grade exploit codenamed
Eternalblue that the NSA used for years to remotely commandeer
computers running Microsoft Windows. Eternalblue, which works
reliably against computers running Microsoft Windows XP through
Windows Server 2012, was one of several potent exploits published in
the most
recent Shadow Brokers release in mid-April.
The Wcry developers have combined the Eternalblue exploit with a
self-replicating payload that allows the ransomware to spread virally
from vulnerable machine to vulnerable machine, without requiring
operators to open e-mails, click on links, or take any other sort of
action.
So-called worms, which
spread quickly amid a chain of attacks, are among the most virulent
forms of malware. Researchers are still investigating how Wcry takes
hold. The awesome power of worms came to the world's attention in
2001 when Code Red managed to infect
more than 359,000 Windows computers around the world in 14 hours.
"The initial
infection vector is something we are still trying to find out,"
Adam Kujawa, a researcher at antivirus provider Malwarebytes, told
Ars. "Considering that this attack seems targeted, it might have
been either through a vulnerability in the network defenses or a very
well-crafted spear phishing attack. Regardless, it is spreading
through infected networks using the EternalBlue vulnerability,
infecting additional unpatched systems.
It's
not clear if the Eternalblue exploit is Wcry's sole means of
spreading or if it has multiple methods of propagating. In an update
that was notable for its unlikely and extremely fortuitous timing,
Microsoft patched the underlying vulnerability in March, exactly four
weeks before the Shadow Brokers' April release published the
weapons-grade NSA exploit. The rapid outbreak of Wcry may be an
indication that many, or possibly all, of the companies hit had yet
to install a critical Windows patch more than two months after it was
releaseOther organizations in
Spain known to be disrupted include telecom Vodafone Espana, the KPMG
consultancy, banks BBVA and Santander, and power company Iberdrola.
The Blackpool Victoria Hospital in the UK reportedly pleaded for
patients to seek
treatment only for life-threatening emergencies after
Wcry crippled its network. Portugal Telecom has also reported
being infected.
Meanwhile, Barts Health Hospital in London is redirecting
ambulances to other facilities.
According to an article
posted by Madrid-based El
Mundo,
85 percent of computers at Telefonica, Spain's dominant telecom, are
affected by the worm, although that figure has not been confirmed.
Officials at Telefonica and Spanish energy companies
Iberdrola and Gas Natural Fenosa have all instructed employees
to shut down computers. While the paper confirmed an attack on
Telefonica, it said it was not yet clear if the other two companies
had been infected or if they ordered the shutdown as a
preventative measure.
Wcry is demanding a
ransom of $300 to $600 in Bitcoin to be paid by May 15, or, in the
event that deadline is missed, a higher fee by May 19. The messages
left on the screen say files will remain encrypted. It's not yet
clear if there are flaws in the encryption scheme that might allow
the victims to restore the files without paying the ransom.
People who have yet to
install the Microsoft fix—MS17-010—should
do so right away. People should also be extremely suspicious of all
e-mails they receive, particularly those that ask the recipient to
open attached documents or click on Web links.
LEAKED NSA MALWARE IS
HELPING HIJACK
COMPUTERS AROUND THE
WORLD
12
May, 2017
In
mid-April, an arsenal of powerful software tools apparently designed
by the NSA to infect and control Windows computers was leaked by
an entity known only as the “Shadow Brokers.” Not even a whole
month later, the hypothetical threat that criminals would use the
tools against the general public has become real, and tens of
thousands of computers worldwide are now crippled by an unknown party
demanding ransom.
An
infected NHS computer in Britain
Gillian
Hann
The
malware worm taking over the computers goes by the names “WannaCry”
or “Wanna Decryptor.” It spreads from machine to machine
silently and remains invisible to users until it unveils itself as
so-called ransomware, telling users all their files have been
encrypted with a key known only to the attacker and that they will be
locked out until they pay $300 to an anonymous party using the
cryptocurrency Bitcoin. At this point, one’s computer would be
rendered useless for anything other than paying said ransom. The
price rises to $600 after a few days; after seven days, if no
ransom is paid, the hacker (or hackers) will make the data
permanently inaccessible (WannaCry victims will have a handy
countdown clock to see exactly how much time they have
left).
Ransomware
is not new; for victims, such an attack is normally a colossal
headache. But today’s vicious outbreak has spread ransomware on a
massive scale, hitting not just home computers but reportedly
healthcare, communications infrastructure, logistics, and government
entities.
Reuters
says “hospitals across England reported the cyber attack was
causing huge problems to their services and the public in areas
affected were being advised to only seek medical care for
emergencies,” and that “the attack had affected X-ray imaging
systems, pathology test results, phone systems and patient
administration systems.”
The
worm has also reportedly reached universities, a major Spanish
telecom,FedEx,
and the Russian
Interior Ministry.
In total, researchers have detected WannaCry infections in
over 57,000 computers across over
70 countries (and
counting–these things move extremely quickly).
According
to experts tracking and analyzing the worm and its spread, this could
be one of the worst-ever recorded attacks of its kind. The security
researcher who tweets and blogs as MalwareTech told The
Intercept “I’ve never seen anything like this with ransomware,”
and “the last worm of this degree I can remember is Conficker.”
Conficker was a notorious Windows worm first spotted in 2008; it went
on to infect
over nine million computers in nearly 200 countries.
Most
importantly, unlike previous massively replicating computer worms and
ransomware infections, today’s ongoing WannaCry attack appears to
be based on an attack developed by the NSA, codenamed
ETERNALBLUE. The U.S. software weapon would have allowed the spy
agency’s hackers to break into potentially millions of Windows
computers by exploiting a flaw in
how certain version of Windows implemented a network protocol
commonly used to share files and to print. Even though Microsoft
fixed the ETERNALBLUE vulnerability in a March software update,
the safety provided there relied on computer users keeping their
systems current with the most recent updates. Clearly, as has always
been the case, many people (including in government) are not
installing updates. Before, there would have been some solace in
knowing that only enemies of the NSA would have to fear having
ETERNALBLUE used against them–but from the moment the agency lost
control of its own exploit last summer, there’s been no such
assurance. Today shows exactly what’s at stake when government
hackers can’t keep their virtual weapons locked up. As security
researcher Matthew Hickey, who tracked the leaked NSA tools last
month, put it, “I am actually surprised that a weaponized malware
of this nature didn’t spread sooner.”
Screenshot
of an infected computer via Avast
The
infection will surely reignite arguments over what’s known as the
Vulnerabilities Equity Process, the decision-making procedure used to
decide whether the NSA should use a security weakness it discovers
(or creates) for itself and keep it secret, or share it with the
affected companies so that they can protect their customers.
Christopher Parsons, a researcher at the University of Toronto’s
Citizen Lab, told The Intercept plainly: “Today’s ransomware
attack is being made possible because of past work undertaken by the
NSA,” and that “ideally it would lead to more disclosures that
would improve the security of devices globally.”
But
even if the NSA were more willing to divulge its exploits rather than
hoarding them, we’d still be facing the problem that too many
people really don’t seem to care about updating their software.
“Malicious actors exploit years old vulnerabilities on a routine
basis when undertaking their operations,” Parsons pointed out.
“There’s no reason that more aggressive disclose of
vulnerabilities through the VEP would change such activities.”
A
Microsoft spokesperson provided the following comment:
“Today our engineers added detection and protection against new malicious software known as Ransom:Win32.WannaCrypt. In March, we provided a security update which provides additional protections against this potential attack. Those who are running our free antivirus software and have Windows updates enabled, are protected. We are working with customers to provide additional assistance.”
Update:
May 12th, 2017 3:45 p.m.
This
post was updated with a comment from Microsoft.
Update:
May 12th, 2017, 4:10 p.m.
This
post was updated with a more current count of the number of affected
countries.






No comments:
Post a Comment
Note: only a member of this blog may post a comment.